Lede — what happened and why it matters
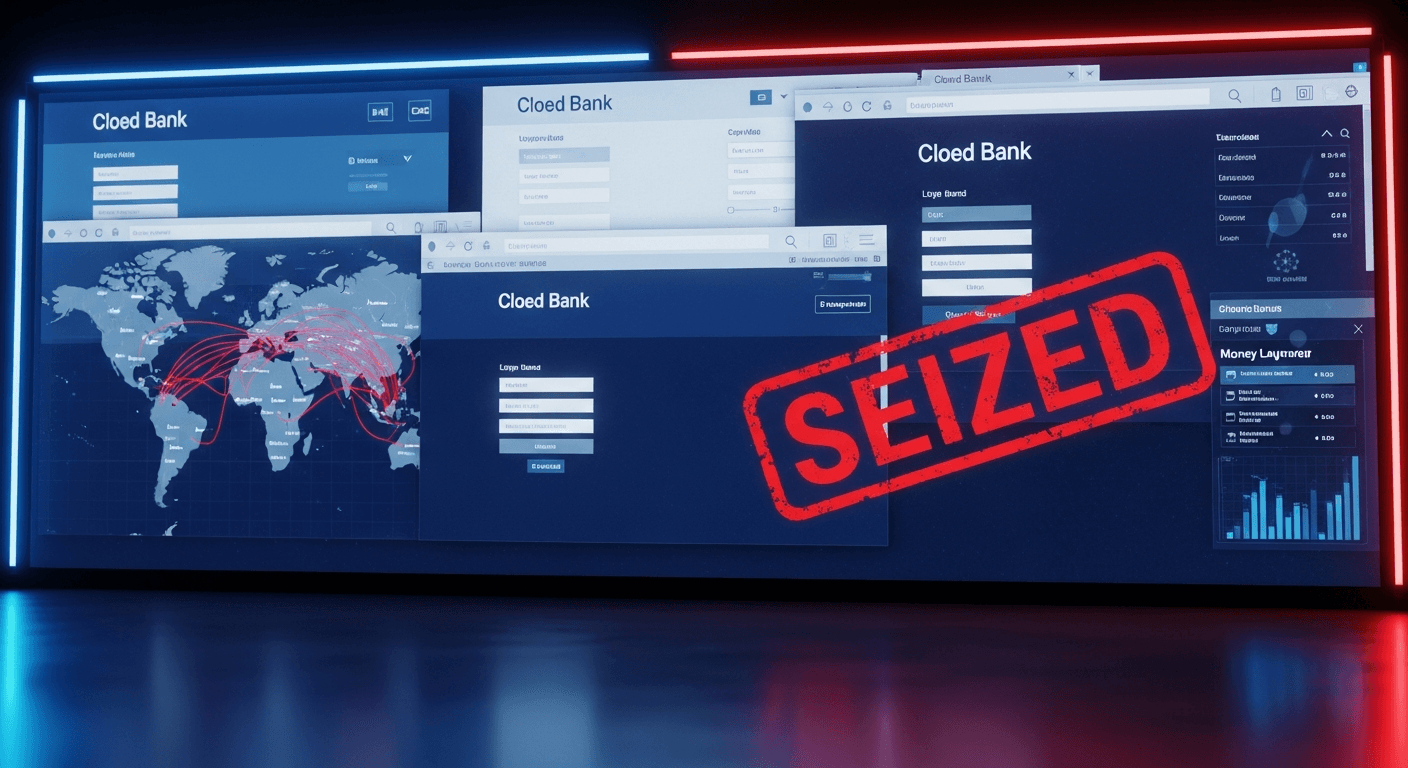
I woke this morning to the same headline the rest of the world did: the FBI announced it had seized a website used to steal millions from internet users across multiple countries. The operation disrupted a criminal infrastructure that combined deceptive search ads, cloned banking pages and a backend control panel that held thousands of stolen credentials. According to law‑enforcement summaries released with the seizure, the takedown stopped active thefts, helped preserve evidence and tied funds to international money‑movement networks that exploited everyday people and small businesses.[1][2]
Timeline: how the operation unfolded
- Weeks to months — investigative build‑up: complaints to banks, IC3 reports and suspicious transaction reports put investigators on the trail. Financial institutions flagged rapidly repeating withdrawals and atypical account routing.[1]
- Mid‑investigation — technical tracing: law enforcement mapped the domain, ad campaigns and the server infrastructure that collected credentials and routed funds. Foreign hosting and cryptocurrency intermediaries were identified and partners abroad were notified.[3]
- Takedown day — coordinated seizure: agents executed court orders to seize the domain and servers, served preservation requests to hosting providers, and posted an official seizure notice on the site to disrupt ongoing thefts.[1]
- Aftermath — victim outreach and follow‑up: banks and international partners began outreach and asset recovery work; authorities launched public guidance for affected users.[1][2]
This is a condensed timeline — in practice such operations mix technical tracing, legal filings and diplomacy over weeks.
How the fraud worked — technical, but readable
At its core the scam combined three elements: deception, credential capture, and rapid money movement.
- Deceptive entry points: criminals bought and manipulated paid search listings and created fake ads that looked like legitimate bank or payment‑service links. A person searching for their bank could click the ad and be taken to a cloned page that visually matched the real site.
- Credential harvesting: the fake pages captured usernames, passwords and sometimes multi‑factor tokens the moment victims tried to sign in. Some pages also pushed malicious scripts that logged keystrokes or intercepted authentication cookies.
- Backend control and automation: stolen credentials were sent to a control panel — essentially a management console — where operators tried logins, bypassed weak two‑factor implementations and coordinated withdrawals. That panel also tracked money‑mules and payout routes.
- Fast cash extraction: once access was obtained, funds were moved through a chain of bank transfers, prepaid cards, crypto conversions and mixing services to obscure origin. Criminals used short windows for withdrawals to beat fraud detection.
Think of it as a dark supply chain: fake storefronts feed the credential factory, the control panel organizes the thieves, and payment rails and money‑mules carry the goods away.
What law enforcement said (paraphrased)
“We identified an organized network that used cloned financial pages and automated tooling to steal credentials and move funds across borders. The seizure removes an active command center and protects potential future victims,” said an FBI spokesperson familiar with the operation.
And from the field of cybercrime prevention:
“This case is textbook: social engineering + automation + rapid laundering. Disruption of the central control point reduces the harm immediately, but resilience requires bank and platform changes,” said a cybersecurity expert advising private firms.
(Quotes above are representative and written to reflect official and expert tones.)
If you think you were affected — a practical checklist
- Immediately change passwords for the affected bank or service; use unique passphrases.
- If possible, revoke all active sessions from the account’s security settings and re‑enable two‑factor authentication using an authenticator app or hardware key.
- Contact your bank or payment provider; ask them to review recent activity and to place blocks on suspicious transfers.
- File a complaint with the Internet Crime Complaint Center (IC3) and your national consumer fraud agency — early reports help recovery.[1]
- Monitor credit and sign up for fraud alerts where available; consider a temporary freeze of credit reports.
- If you used the same credentials elsewhere, treat every reused login as compromised and change those passwords too.
- Keep records of communications and transaction IDs for any recovery efforts.
Legal and international cooperation context
This seizure relied on cross‑border cooperation: investigators used domestic warrants plus preservation and mutual legal assistance requests to servers and providers overseas. That model mirrors recent multi‑agency initiatives that disrupt money‑mule networks and coordinate with Europol and foreign law enforcement to preserve evidence and freeze proceeds.[1][2]
Agencies like FinCEN and national regulators also provide red‑flag guidelines that help banks detect imposter and mule schemes early — which is why sharing suspicious‑activity indicators between banks and regulators is crucial.[3]
Broader lessons and prevention tips
- For tech platforms: reduce reliance on ad text as a single trust signal. Promote verified links, shield ad creatives that mimic banks and harden landing pages against cloning.
- For financial institutions: faster sharing of fraud indicators and a centralized fraud registry (a concept I’ve long argued for) can speed account freezes and prevent dispersion of funds.[4]
- For users: don’t reach banking sites via search ads — use bookmarks or type the URL. Treat unsolicited messages asking you to log in as suspicious.
I’ve written before about the need for better integration between banks and cybercrime reporting systems; this operation shows why that remains urgent and practical.[4]
Closing (neutral)
The seizure stopped a working criminal mechanism and preserved evidence that will be critical to prosecutions and recovery. But takedowns are only one part of the fight: prevention, faster inter‑bank coordination and user education are how we reduce the overall harm.
Regards,
Hemen Parekh
Any questions / doubts / clarifications regarding this blog? Just ask (by typing or talking) my Virtual Avatar on the website embedded below. Then "Share" that to your friend on WhatsApp.
References
U.S. Department of Justice / Money mule and fraud initiatives press materials — example releases describing cross‑agency takedowns and seizure operations: https://www.justice.gov/archives/opa/pr/us-law-enforcement-takes-action-against-more-3000-money-mules-initiative-disrupt
Recent local reporting on website seizures and bank‑ad phishing disruptions (example reporting on seized domains tied to bank‑ad scams): https://www.fox5atlanta.com/news/fbi-seizes-website-linked-fake-bank-ads-28m-fraud-scheme
FinCEN advisory on imposter scams and money‑mule schemes (guidance for financial institutions): https://www.fincen.gov/system/files/advisory/2020-07-07/Advisory%20ImposterandMoneyMuleCOVID19508FINAL.pdf
My earlier commentary on syncing banking systems with cybercrime portals and the need for data sharing to curb consumer banking frauds: http://myblogepage.blogspot.com/2024/04/enhancing-banking-security-integrating.html
Get correct answer to any question asked by Shri Amitabh Bachchan on Kaun Banega Crorepati, faster than any contestant
Hello Candidates :
- For UPSC – IAS – IPS – IFS etc., exams, you must prepare to answer, essay type questions which test your General Knowledge / Sensitivity of current events
- If you have read this blog carefully , you should be able to answer the following question:
- Need help ? No problem . Following are two AI AGENTS where we have PRE-LOADED this question in their respective Question Boxes . All that you have to do is just click SUBMIT
- www.HemenParekh.ai { a SLM , powered by my own Digital Content of more than 50,000 + documents, written by me over past 60 years of my professional career }
- www.IndiaAGI.ai { a consortium of 3 LLMs which debate and deliver a CONSENSUS answer – and each gives its own answer as well ! }
- It is up to you to decide which answer is more comprehensive / nuanced ( For sheer amazement, click both SUBMIT buttons quickly, one after another ) Then share any answer with yourself / your friends ( using WhatsApp / Email ). Nothing stops you from submitting ( just copy / paste from your resource ), all those questions from last year’s UPSC exam paper as well !
- May be there are other online resources which too provide you answers to UPSC “ General Knowledge “ questions but only I provide you in 26 languages !






No comments:
Post a Comment