Executive summary
I’ve written this practical guide to help policymakers, compliance officers, business leaders and informed citizens understand how to operationalise the Digital Personal Data Protection (DPDP) Act in their organisations. The DPDP Act creates a new compliance landscape in India — it’s principle-driven, consent-focused and phased in. Below I set out a pragmatic roadmap (governance, data mapping, consent, DPIAs, contracts, security, breach response, record keeping, training, rights handling, vendor management and cross-border transfers), suggested timelines and KPIs, common pitfalls and ready-to-use templates you can adapt today.
About the author
Connect with Hemen Parekh (hcp@recruitguru.com).
Background: what the DPDP Act requires (concise)
- Scope: The DPDP Act applies to processing of digital personal data collected in digital form or digitised later, and has extraterritorial reach where processing relates to offering goods/services to people in India.MEITY Act PDF
- Legal basis: Consent is the core legal basis for processing; certain legitimate uses are carved out (employment, legal obligations, emergencies).
- Rights: Data principals have rights to access, correction, erasure (subject to grounds), grievance redressal and to nominate someone to act for them.
- Significant Data Fiduciaries: The government can designate ‘significant’ fiduciaries with extra obligations — DPOs, auditors, periodic DPIAs.
- Enforcement: Data Protection Board of India (DPB) will adjudicate breaches and impose penalties; fines can be material (schedules show high maxima for severe lapses).PRS / DSCI summaries
Why act now
The Act is being implemented in phases; many organisations will be expected to demonstrate readiness well before any final enforcement dates. Organisations that act early reduce legal, reputational and operational risk and gain customer trust.
Implementation roadmap: step-by-step
1) Governance and program setup (0–30 days — high priority)
- Sponsor and steering: Appoint a senior executive sponsor (board level or CISO/GC). Establish an implementation steering committee with Legal, IT, Security, HR, Product, Marketing and Compliance.
- Program plan: Create a 6–12 month project plan with milestones (see suggested timelines below).
- Roles & responsibilities: Identify the Data Fiduciary owner, DPO (if required / for SDFs), IT lead, Privacy Champion in each business unit and a legal escalation path.
2) Data mapping & inventory (0–90 days — critical)
- Create a central registry of data flows: what data is collected, purpose, storage location, retention, access lists and transfers (internal & external).
- Tag data by sensitivity and by whether processing rests on consent.
- Tools: Use automated discovery tools for structured systems; complement with interviews for manual processes.
3) Consent & notice frameworks (30–120 days)
- Standardise consent language: simple, purpose-specific, granular, withdrawable. Store consent records with timestamps and provenance.
- Implement layered notices (short summary + detailed policy) at point of collection and in user accounts.
Sample short consent language (template)
- "I agree to [Company] using my name, email and transaction history to provide and personalise the service, send account notices and offers. I can withdraw consent anytime via Account Settings or by emailing privacy@[yourdomain]."
4) Data Protection Impact Assessments (DPIAs) (30–120 days)
- Create a DPIA policy and checklist. Conduct DPIAs for high-risk processing (profiling, large-scale data profiling, children’s data, new AI systems).
DPIA checklist (short)
- Purpose & lawful basis identified
- Data minimisation review
- Risk to individuals (likelihood & severity)
- Technical & organisational mitigations
- Residual risk and decision (accept / change / stop)
- Review schedule and owner
5) Contracts & third-party management (30–120 days)
- Update processor/processor agreements to include DPDP obligations (purpose limitation, security standards, audit rights, sub-processor controls, deletion obligations, assistance for rights requests).
- Maintain an approved vendor list with DPIA outcomes and security attestations.
6) Security measures & data lifecycle controls (Ongoing — start immediately)
- Implement least privilege, encryption at rest/in transit, logging, MFA, regular patching and vulnerability management.
- Retention policy: map legal/operational retention to deletion schedules; automate data purging where possible.
7) Data breach preparedness & response (30–90 days)
- Create an incident response plan aligned to DPDP obligations: detection, containment, assessment of harm, notification to DPB and affected data principals in prescribed format and timelines.
- Tabletop exercises quarterly.
Breach notification timeline (template)
- T+0–24h: Detect & contain. Notify internal incident lead.
- T+24–72h: Assess scope and whether DPB + data principals must be notified (follow regulatory guidance). Prepare communications.
- T+72h+: Notify DPB and affected principals with prescribed information: nature of breach, data types, mitigation steps and contact point.
8) Record-keeping & evidence (30–120 days)
- Maintain records of processing activities, consents, DPIAs, breach logs, vendor agreements and audit trails for at least the retention period required by law or policy.
9) Training & awareness (ongoing)
- Role-based training: executives, developers, sales, HR and frontline customer service.
- Monthly micro-learning on consent, data minimisation and incident reporting.
10) Data subject rights handling (30–90 days)
- Build a simple rights-request intake system (web form + verification steps) and SLA-backed workflows for access, correction and erasure requests.
- Log, track and report: time to respond and resolution quality.
11) Cross-border transfers (30–120 days)
- Map outbound transfers. If the recipient country is restricted by notification from the Government, update flows. Use contractual safeguards and ensure legal basis for transfer.
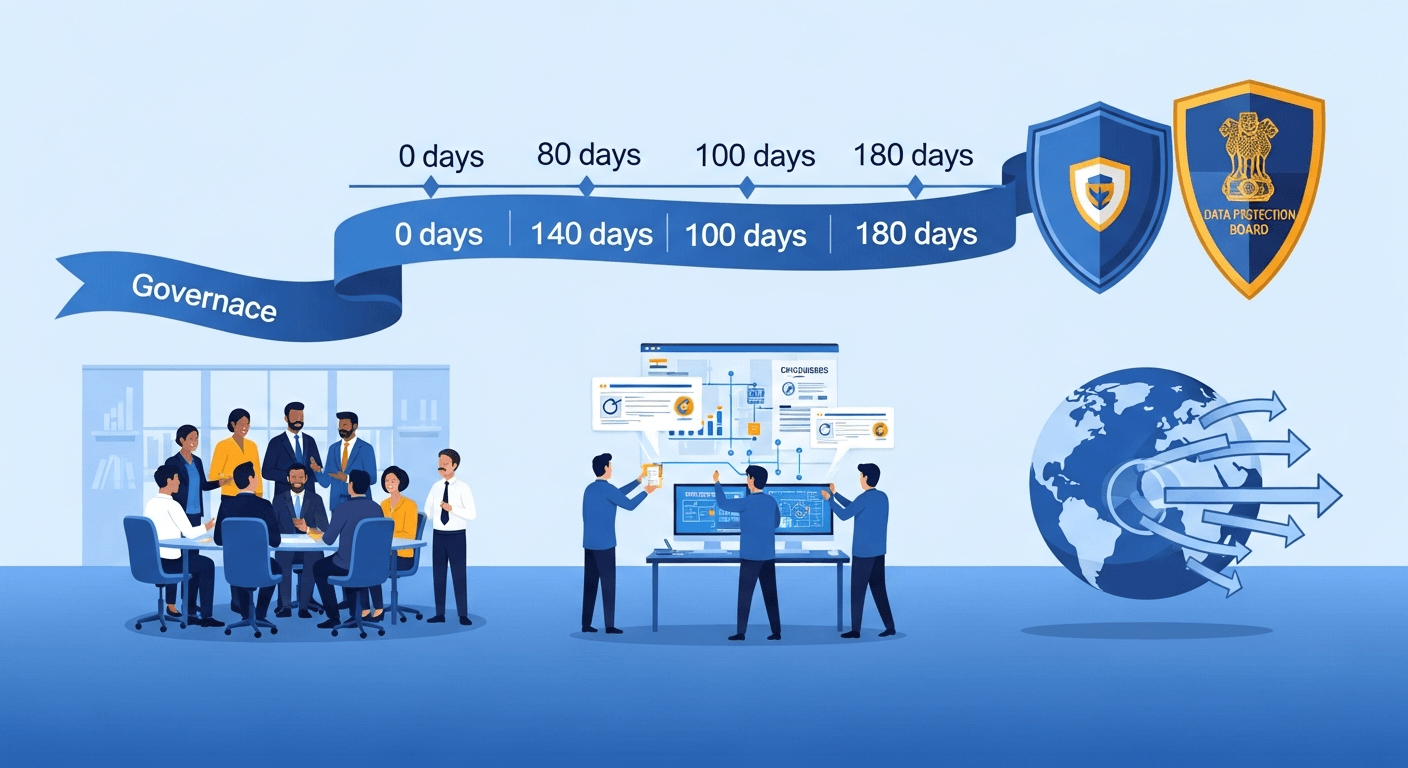
Timelines & prioritisation (practical)
- Immediate (0–30 days): Program governance, top-10 data mapping, basic security hardening, consent audit.
- Short term (30–90 days): DPIAs for new/critical systems, vendor contract updates, breach response plan, rights intake mechanism.
- Medium term (90–180 days): Automate retention/deletion, embed privacy in product processes, staff training cadence, external audit readiness.
- Ongoing: Continuous monitoring, periodic DPIA refresh, board reporting.
Common pitfalls and how to avoid them
- Pitfall: Treating DPDP as a legal-only problem. Fix: build cross-functional program and technical controls.
- Pitfall: Over-reliance on manual logs and spreadsheets. Fix: invest in automated discovery, consent management and rights portals.
- Pitfall: Vague consent language and buried notices. Fix: adopt layered notices and explicit, purpose-specific consent.
- Pitfall: Neglecting vendor risk. Fix: standardise contracts and continuous vendor monitoring.
Simple KPIs to measure compliance (internal)
- % of data assets mapped and classified.
- % of consented records with verifiable consent metadata.
- Number of DPIAs completed for new projects / total required.
- Mean time to detect (MTTD) and mean time to respond (MTTR) for incidents.
- % of data subject requests closed within SLA (e.g., 30 days).
- % of third parties with up-to-date contracts and security attestations.
- Number of training completions and phishing simulation pass rate.
Templates & examples (copy and adapt)
- Consent language: see the short consent example above. Keep it simple and provide withdraw steps.
- DPIA checklist: see the short checklist above; expand with scoring for likelihood/severity.
- Breach notification timeline: see breach timeline. Keep templates for regulator and consumer communications ready.
Role of regulators and penalties
- The Data Protection Board of India will investigate complaints and impose penalties based on severity, duration and mitigation steps. Penalties can be significant for serious security failures. The government can also classify fiduciaries as “significant” and impose higher obligations.
- Work with regulators: subscribe to DPB guidance, use industry associations for clarifications and maintain transparent communication post-incident.
Expected business impacts
- Short term: Implementation effort, legal and compliance spend, potential product updates and vendor renegotiations.
- Medium term: Greater operational discipline, stronger data governance, reduced breach risk.
- Strategic: Increased customer trust and competitive differentiation for organisations that treat privacy as a product feature. Non-compliance risks include fines, reputational damage and loss of customer trust.
Short case studies (illustrative)
- FinTech startup: Prioritised mapping customer onboarding flows, automated consent capture and deletion, and updated processor contracts. Result: streamlined rights handling and reduced audit effort by 60%.
- Platform company: Conducted DPIAs for new profiling engine, adjusted retention windows and introduced opt-outs; this reduced legal risk and improved retention of privacy-sensitive customers.
Where I’ve written before
I’ve written earlier on the foundational pillars of data protection — those ideas about minimisation, meaningful consent and accountability remain relevant as we implement the DPDP Act.My earlier reflections on the 7 pillars of data protection law
Closing: pragmatic next steps for leaders
- Board: Request a DPDP readiness briefing this quarter (top risks, budget ask, timelines).
- CISO/GC: Begin the top-10 data mapping and run a DPIA for any high-risk product in flight.
- Product/Engineering: Add consent and withdraw flows to product backlog and instrument audit logs.
- HR/Training: Start role-based privacy training now.
If you start with governance, map your most critical data, and operationalise consent, the rest becomes engineering and policy execution. The DPDP Act is an opportunity to build trust into digital services — done well it becomes a business advantage.
Regards,
Hemen Parekh (hcp@recruitguru.com)
Any questions / doubts / clarifications regarding this blog? Just ask (by typing or talking) my Virtual Avatar on the website embedded below. Then "Share" that to your friend on WhatsApp.
Get correct answer to any question asked by Shri Amitabh Bachchan on Kaun Banega Crorepati, faster than any contestant
Hello Candidates :
- For UPSC – IAS – IPS – IFS etc., exams, you must prepare to answer, essay type questions which test your General Knowledge / Sensitivity of current events
- If you have read this blog carefully , you should be able to answer the following question:
- Need help ? No problem . Following are two AI AGENTS where we have PRE-LOADED this question in their respective Question Boxes . All that you have to do is just click SUBMIT
- www.HemenParekh.ai { a SLM , powered by my own Digital Content of more than 50,000 + documents, written by me over past 60 years of my professional career }
- www.IndiaAGI.ai { a consortium of 3 LLMs which debate and deliver a CONSENSUS answer – and each gives its own answer as well ! }
- It is up to you to decide which answer is more comprehensive / nuanced ( For sheer amazement, click both SUBMIT buttons quickly, one after another ) Then share any answer with yourself / your friends ( using WhatsApp / Email ). Nothing stops you from submitting ( just copy / paste from your resource ), all those questions from last year’s UPSC exam paper as well !
- May be there are other online resources which too provide you answers to UPSC “ General Knowledge “ questions but only I provide you in 26 languages !






No comments:
Post a Comment